John the Ripperis a fast password cracker, available for many operating systems.Its primary purpose is to detect weak Unix passwords,although Windows LM hashesand a number of other password hash types are supported as well.John the Ripper is free and Open Source software,distributed primarily in source code form. John the Ripper Pro builds upon the free John the Ripper to delivera commercial product better tailored for specific operating systems.It is distributed primarily in the form of 'native' packages forthe target operating systems. |
|
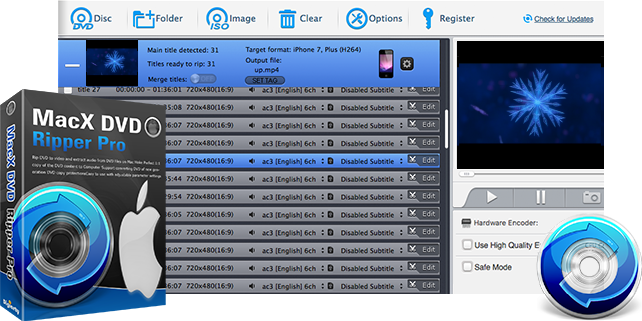
Download Jack the Ripper for Mac to can you clear the name of the reporter Bert, suspected of being Jack the Ripper. The second ripper on our list is the MacX DVD ripper from Digiarty Software. There are available in two versions – Pro and free edition. The MacX DVD Ripper Pro was rated as the best Mac DVD ripper by our editor. The free version also has all the program features but with few limitations. Download John the Ripper - A fast passcode decrypting utility that was designed to help users test the strength of their passwords or recover lost passphrases.
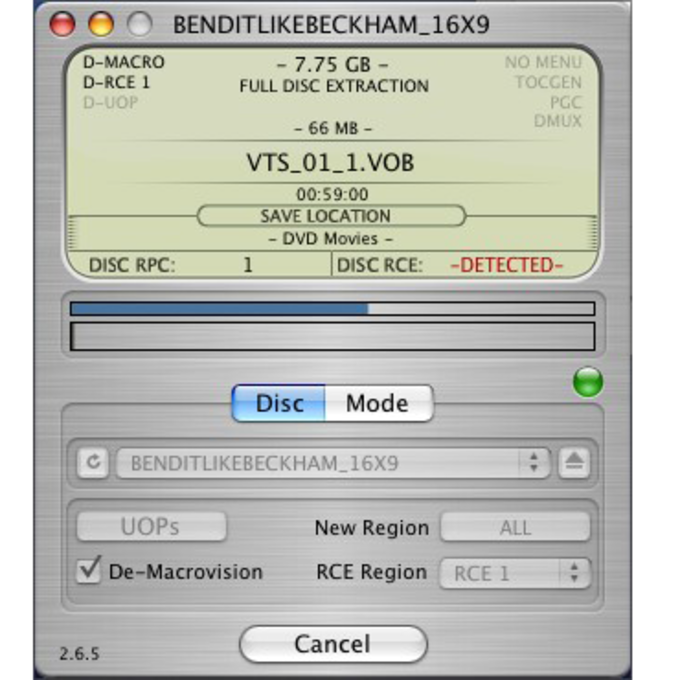
- Since you are familiar with the use of the program, take a look at the guide below on how to rip DVD on Mac 10.10 Yosemite with this latter program MacTheRipper alternative. Free download and install the Best MacTheRipper Alternative on your Mac. Launch it and import your dvd movie file into it.
- If you are in search of an awesome open source website ripper that will help you to get a whole site downloaded, Darcy ripper will be the right choice. Along with the website, web related elements can be downloaded on the go. Darcy Ripper is highly efficient, and will allow you to.
John the Ripper Pro is currently availablefor Linux on x86 and x86-64 (x64) systems,with support for the latest Intel and AMD processor features such as SSE2,andfor Mac OS X on both Intel and PowerPC Macs,making use of SSE2 and AltiVec acceleration, respectively.
Proceed to John the Ripper Pro homepage for your OS:
- On Windows, consider Hash Suite(developed by a contributor to John the Ripper)
Support for certain other operating systems and processor architectures isplanned.If your OS is not supported yet,please use the Quick Comment field at the bottom of this web page torequest support for your OS;be sure to explicitly indicate your interest in purchasinga copy and license, and provide your e-mail address and desired price.Please note that support for a new OS in Pro versions ofJohn the Ripper may only be added in response to commercial demand.Meanwhile, feel free to explore thecross-platform and free version of John the Ripper.
John the Ripper Procurrently supports the following password hash types(and more are planned):
- Traditional DES-based Unix crypt(3) -most commercial Unix systems (Solaris, AIX, ...),Mac OS X 10.2, ancient Linux and *BSD
- 'bigcrypt' - HP-UX, Tru64 / Digital Unix / OSF/1
- BSDI-style extended DES-based crypt(3) - BSD/OS, *BSD (non-default)
- FreeBSD-style MD5-based crypt(3)- older Linux, FreeBSD, NetBSD, Cisco IOS, OpenBSD (non-default)
- OpenBSD-style Blowfish-based crypt(3)- OpenBSD, some Linux, other *BSD and Solaris 10+ (non-default)
- SHA-crypt (sha512crypt and sha256crypt) - newer Linux
These are supported when running on a Linux system with glibc 2.7+ (any recent system) - Kerberos AFS DES-based hashes
- LM (LanMan) DES-based hashes -Windows NT/2000/XP/2003, Mac OS X 10.3
- NTLM MD4-based hashes -Windows (all versions)
- Mac OS X 10.4 - 10.6 salted SHA-1 hashes
- Mac OS X 10.7 salted SHA-512 hashes (new in 1.8.0 Pro, currently available for Linux only)
You can browse the generic documentation for John the Ripper online.Also relevant is ourpresentation on the history of password security.
747525 |
John the Ripper is an Open Source password security auditing and password recovery tool available for many operating systems.John the Ripper jumbo supports hundreds of hash and cipher types, including for: user passwords of Unix flavors(Linux, *BSD, Solaris, AIX, QNX, etc.), macOS, Windows, 'web apps' (e.g., WordPress), groupware (e.g., Notes/Domino), anddatabase servers (SQL, LDAP, etc.);network traffic captures (Windows network authentication, WiFi WPA-PSK, etc.);encrypted private keys (SSH, GnuPG, cryptocurrency wallets, etc.),filesystems and disks (macOS .dmg files and 'sparse bundles', Windows BitLocker, etc.),archives (ZIP, RAR, 7z), and document files (PDF, Microsoft Office's, etc.)These are just some of the examples - there are many more. |
|
John the Ripper is free and Open Source software,distributed primarily in source code form.If you would rather use a commercial product, please considerJohn the Ripper Pro,which is distributed primarily in the form of 'native' packagesfor the target operating systems and in general is meant to be easier toinstall and use while delivering optimal performance.
Proceed to John the Ripper Pro homepage for your OS:
Download the latest John the Ripper jumbo release(release notes) or development snapshot:
Run John the Ripper jumbo in the cloud (AWS):
Download the latest John the Ripper core release(release notes):
|
These and older versions of John the Ripper, patches, unofficial builds, and many other related files are alsoavailable from the Openwall file archive.
You can browse the documentation for John the Ripper core online, including asummary of changes between core versions.Also relevant is ourpresentation on the history of password security.
There's a collection of wordlists for use with John the Ripper.It includes lists of common passwords, wordlists for 20+ human languages, and files with the common passwords andunique words for all the languages combined, also with mangling rules applied and any duplicates purged.
yescrypt and crypt_blowfishare implementations of yescrypt, scrypt, and bcrypt - some of the strong password hashes also found in John the Ripper -released separately for defensive use in your software or on your servers.
passwdqc is a proactive password/passphrase strength checking and policy enforcement toolset,which can prevent your users from choosing passwords that would be easily cracked with programs like John the Ripper.
We can help you integrate modern password hashing withyescrypt or crypt_blowfish,and/or proactive password strength checking withpasswdqc,into your OS installs, software, or online services.Please check out our services.
There's a mailing list where you can share your experience with John the Ripper and ask questions.Please be sure to specify an informative message subject wheneveryou post to the list(that is, something better than 'question' or 'problem').To subscribe, enter your e-mail address below or send an empty message to<john-users-subscribe at lists.openwall.com>.You will be required to confirm your subscription by 'replying'to the automated confirmation request that will be sent to you.You will be able tounsubscribeat any time and we will not use your e-mailaddress for any other purpose or share it with a third party.However, if you post to the list, other subscribers and thoseviewing the archives may see your address(es) as specified on your message.The list archive is availablelocally and viaMARC.Additionally, there's alist of selected most useful and currently relevant postings on thecommunity wiki.
Contributed resources for John the Ripper:
|

John the Ripper is part ofOwl,Debian GNU/Linux, Fedora Linux, Gentoo Linux, Mandriva Linux, SUSE Linux,and a number of other Linux distributions.It is in the ports/packages collections of FreeBSD, NetBSD, and OpenBSD.
Handbrake For Mac
John the Ripper is a registered project withOpen Huband it is listed atSecTools.
Mactheripper 4 Free Download
30720837 |